In July 2018, Google’s started marking non-HTTPS sites as ‘not secure’ in the Chrome browser. Meaning if you open a website that doesn’t support HTTPS right of the box, you will see “Not Secure” warning with a red triangle in the URL box. This makes sure no one, including your ISP, knows what you are browsing. However, the DNS queries were left far behind and until DNS-over-HTTPS was introduced in October 2018. It’s been a year and major tech giants like Google, Microsoft, Mozilla has been testing DoH to integrate into their product.
What is DoH?
DNS-over-HTTPS (DoH) ensures that your DNS queries are sent over HTTPS. This simply means the URL entered in your browser’s address bar will be sent in the encrypted format. Formerly, whatever DNS name or URL you enter in your browser’s address bar was sent to the DNS servers in plain text. This made it easy for your ISP and network sniffers to identify the websites you are visiting. The data that you send to these websites was still encrypted, however, the DNS queries weren’t.
For instance, if you are scrolling Facebook.com and visiting certain Facebook profiles, your ISP or public networks cannot make out that the profiles you are visiting. However, they can still figure out that you are visiting Facebook.com as the DNS search queries are in plain text. But, now with DNS-over-HTTPs, your ISP can’t figure out that you are opening Facebook.com
How to enable it?
Chrome
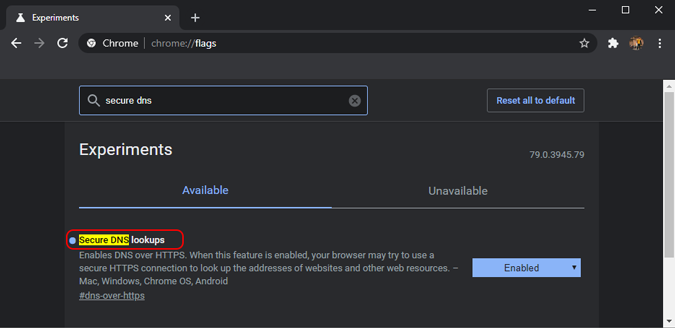
With the recent Chrome 79 update, Google has said that it will integrate DoH by default in 1% of the user’s search. However, you can force Google Chrome to use DNS-over-HTTPS every single time by enabling the Secure DNS lookups flag. Enabling this flag ensures that your web address search within Chrome will be encrypted. The only caveat is that you should be using a DNS server that supports DoH like Google DNS, OpenDNS, or Cloudflare DNS.
Firefox
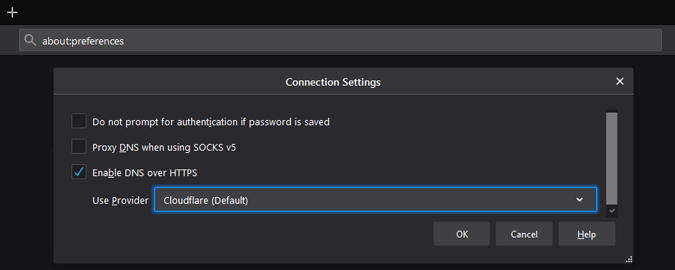
Mozilla enabled DoH features way back at the start of 2019 for every Firefox user. DoH, by default, isn’t enabled out of the box. You would have to jump down to the Preferences section to enable it.
The functioning in Firefox is slightly different from the Google Chrome browser, you can have a separate DNS server for the browser itself while a separate DNS server for the entire system. Once you enable it, DoH in Firefox starts using Cloudflare as the DNS server. In case you want to set up a custom DNS server, you can choose through the dropdown and enter the IP address.
Microsoft has promised that it would be coming in with the DNS-over-HTTPs solution for the entire Operating system out of the box. This would ensure DNS queries sent by the desktop applications are also encrypted. However, this won’t work if you change the DNS server to a public DNS server or your ISPs.
Testing DNS-over-HTTPs
Before I pen down this article, I tried to test the water with Google Chrome. DoH in Google Chrome is still in testing and available only through the Chrome flags. I tried to analyze my laptop’s Wi-Fi packets using a packet analyzer app like Wireshark. I analyzed the packets before and after enabling DoH.
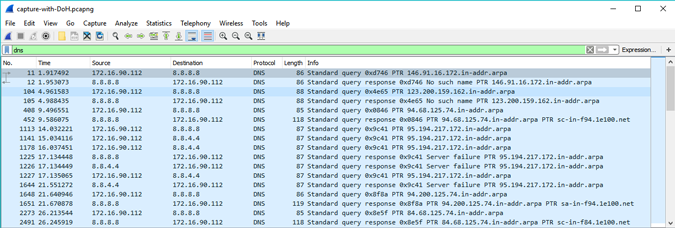
Surprisingly or thankfully, when you turn on the DoH for Google Chrome, WireShark is not able to detect the DNS queries sent by Google Chrome. In the following screenshot, the DNS query request sent from my system to the Google DNS server is visible. However, you cannot see the packets with the URL name.
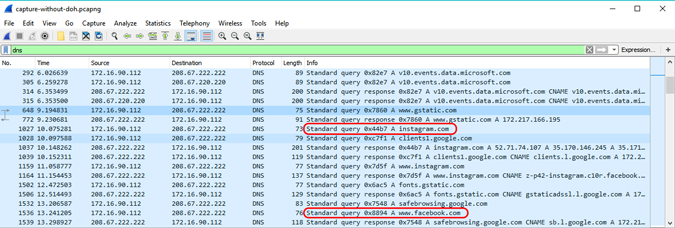
Next, when I turn off the DoH and switched to the OpenDNS server. Hence, you can see the DNS query packets visible in the Wireshark scan. The query from my system to the Google DNS server is visible with the exact URL of the website I was looking for. Without DoH, this is how network sniffers or your ISP can see the websites you are visiting.
For issues or concerns regarding DNS-over-HTTPs, let me know in the comments below.
Also Read: How to Change DNS Server – An In-Depth Guide for All Platforms