Ever wondered whether the charging stations and USB ports you see in public areas are safe or are more harmful in more ways than one? Unsuspecting users are falling prey to a new hacking trick called Juice Jacking Here is everything you need to know about juice jacking and how it works.
Table of Contents
Juice Jacking in the Real World
Juice Jacking is a form of cyber attack that refers to unauthorized access, stealing data, or uploading malware to connected devices (primarily smartphones and laptops) when charging via public USB charging ports and kiosks. Some examples include an airport or a restaurant.
The type of cyber attack is not new altogether having originated more than a decade ago. Juice Jacking was revealed in 2011 DEFCON as a concept. It showed that it is possible to steal data while users are charging their smartphones. Since then, manufacturers have taken many data privacy and protection steps like data access and camera permissions, but juice jacking remains a threat.
Repercussions of Juice Jacking
The talking point of Juice Jacking is that someone with malicious intent can access your data, sensitive or otherwise, from your smartphone (iPhone and Android) just by plugging in an infected charging source. If you’re someone who travels a lot and has to use public charging points at random locations, then you’re more prone to this cyber attack.
Using public charging points means not only your data is at stake but tracking and monitoring spyware can also be uploaded onto your device. With this comes the question, Is it all worth it?
Here is what FBI Denver said in a tweet on their official X (formerly Twitter) account.
Avoid using free charging stations in airports, hotels or shopping centers. Bad actors have figured out ways to use public USB ports to introduce malware and monitoring software onto devices. Carry your own charger and USB cord and use an electrical outlet instead.
Ways to Avoid Juice Jacking
The best way to save yourself from being a victim of juice jacking would be to completely avoid using any public ports or charging points as mentioned by the federal authority. But still, if you have to use them in emergencies then we have compiled a list of different ways for you to avoid the cyber attacks associated with them.
1. Carry your wall charger adapters and USB cables with you. This way you won’t be targeted and can charge anywhere. Here is our pick for the best chargers for your iPhone 15 series.
2. If possible, carry a power bank with you at all times. You can use that to charge your devices. If the power bank gets discharged, then you can charge it from the public charging ports. This way you won’t be targeted but still can charge your stuff. Here’s a guide on the best accessories to get with your iPhone 15 series.
3. You can use a reputed charging-only USB cable which will only charge your smartphone and not allow data transfers. But do remember that these charging-only cables are not as fast as your usual charging cables. However, they are far more secure.
4. If you’re on a road trip then be sure to take along a car charger. This way you won’t have to depend on any public charging ports. Stay charged up on the move!
5. While we don’t prefer wireless charging due to the excessive heat generated, it can be your savior in disguise. Because wireless charging doesn’t allow data transfer, you can easily charge your smartphone anywhere using a compatible wireless charger.
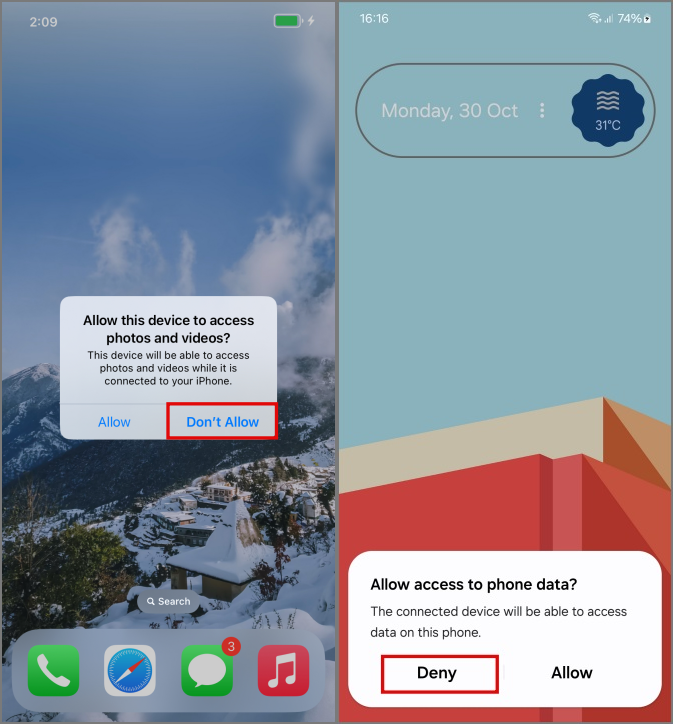
6. If you have to use these public charging stations, ensure you’re only allowing charging. Choose Don’t Allow or Deny any access to your photos, videos, or data if asked anytime during charging. This is how the pop-up for the same looks on the iPhone and Android.
Avoid Public Chargers
Now you know how serious Juice Jacking is and what it can do if you’re not vigilant enough. The best way to protect yourself from juice jacking is by using your adapters, cables, and powerbanks.
Talking about data theft, are you also worried about iPhone theft? Not so uncommon these days. A new iPhone setting can protect your financial apps and data from thieves’ prying eyes. Here is everything you need to know about stolen device protection feature on iPhones.